
Hardware security modules are specialized computing devices designed to securely store and use cryptographic keys. Let’s break down what HSMs are, how they work, and why they’re so important to public key infrastructure
Demand for hardware security modules (HSMs) is booming. Data from Entrust’s 2021 Global Encryption Trends Study shows that HSM usage has been steadily increasing over the last eight years, increasing from 26% in fiscal year 2012 to 49% in 2020. According to data from 360 Market Updates, the HSM market is expected to reach $2.75 billion by the end of 2026.
What is an HSM and what does it do? Why are so many companies using HSMs? And what are the practical uses for HSMs in enterprise environments?
Let’s hash it out.
What Is a Hardware Security Module (HSM)? An HSM Definition & Explanation

Encrypted data isn’t secure if the keys you use to encrypt it are exposed — this is where HSMs can save the day. Hardware security modules (HSMs) are tamper- and intrusion-resistant hardware components that organizations use to protect and store their cryptographic keys while still making them available for use by authorized users. Their purpose is to control access and limit risk to your company’s sensitive private keys.
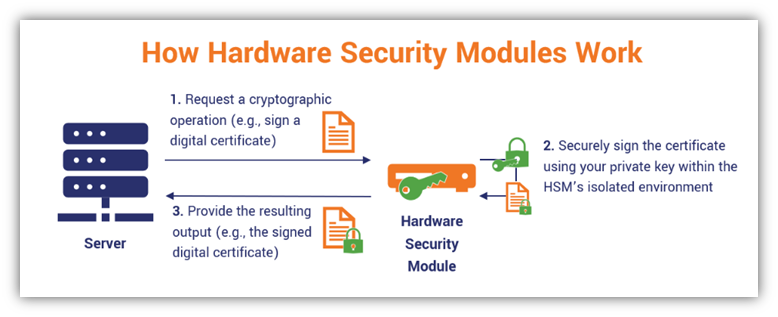
HSMs enable your employees to use of your organization’s private keys without needing direct access to them. Basically, your software (for example, hosted on a web server) can execute cryptographic functions and authentication without loading a copy of your private key into memory on your web server (where it could be vulnerable to attack). The cryptographic functions are all done within the confines of an HSM’s secure environment. Performing these operations within this secure little bubble keeps your sensitive data from becoming compromised by keeping the private keys hidden away in a secure location.
To better understand this concept, think of an HSM like a vending machine. A vending machine stores drinks and food items within an isolated internal environment. It’s designed to accept user inputs (i.e., your item selections) and generate outputs (i.e., pop out a tasty snack), and you can’t access the inside of the vending machine or alter its functions.
Similarly, an HSM accepts user inputs and generates outputs (such as signed certificates or software) without users (or applications) seeing, accessing, or altering your cryptographic keys. That’s because its functions are executed within the confines of its secure environment, and no key can be wholly exported, extracted or removed from an HSM in a readable format. So, like a vending machine, you can use it to get your desired output but you can’t see or access the internal workings of the device and all of its individual components that made it possible.
Here’s a quick overview of how hardware security modules work:
How Using an HSM Can Help Your Business
You may be wondering why you need to use a hardware security module at all. I mean, why should you go through the hassle and cost of setting up an HSM when you can simply use your web server’s built-in functionalities?
Well, for one thing, an HSM provides significantly more secure key storage than what you’d get from using a traditional web server. When companies use their web servers to run many applications, this can result in vulnerabilities that cybercriminals can exploit. HSMs are devices with limited usages and attack vectors. This is why:
- Public certificate authorities and registration authorities use these devices to create, store and manage their sensitive keypairs. (Note: They generally store the root CA offline to keep it as secure as possible.)
- Companies with private PKIs use these devices to use and store the keys they use to sign their PKI certificates, software code and documents.
Using an HSM helps you secure your private code signing keys and avoid exposure issues like what HashiCorp faced earlier this year. On April 22, HashiCorp informed customers that the GPG private key they use to sign official product downloads and updates was exposed as the result of a third-party (Codecov) security incident.
Basically, the crux of the situation is that an unauthorized user exploited a vulnerability that gave them the ability to export sensitive data from Codecov’s continuous integration (CI) environments. HashiCorp’s CI environment — which housed the company’s GPG private key and other “sensitive secrets” among — were among those exposed CI environments. If HashiCorp stored their key in a secure HSM instead of the CI, then it wouldn’t have been exposed.
How HSMs Improve IT and Data Security
There are also many other purposes and uses that HSMs serve in terms of PKI and general cybersecurity. You can use an HSM to:
- Store and protect all of your cryptographic keys throughout their lifecycles. HSMs are generally standalone network-connected devices that are separate from your servers. This helps to keep your keys secure through all lifecycle stages — from generation all the way through their eventual destruction or revocation.
- Generate the most cryptographically strong keys for your PKI. HSMs have built-in true random number generators (TRNGs) that provide randomness and unpredictability.
- Protect the security of your keys through “zeroization.” Because HSMs are tamper-resistant devices (both for logical and physical attacks), they’re built to erase or destroy all stored cryptographic data to prevent compromise.
- Secure your organization’s cryptographic operations and services. Restricting these functions (such as signing PKI certificates, applications and documents) to occur only within the secure, stand-alone environment of the HSM helps to prevent key exposure.
- Improve server performance via load balancing. HSM devices are stripped-down, standalone devices that can take on the responsibility of performing operations that otherwise bog down your servers. Some HSMs are equipped to act as web traffic accelerators by offloading cryptographic operations.
- Protect your keys from insecure extractions that can lead to compromise. “Wrap” or encrypt your encryption keys to prevent them from being extracted in plaintext format.
- Secure the keys for your development, testing and production environments. An HSM protects the private PKI keys used by the software and systems relating to your internal production and testing environments so these systems can use them without needing direct access to them. (Note: use a separate HSM for each environment to avoid data security risks — never use the same HSM across multiple environments).
- Ensure compliance with data security regulations and simplify audit processes. HSMs are typically validated hardware components that ensure compliance because they meet specific industry standards. They also provide tamper-resistant logs that inform you about:
- what cryptographic operations they’re used to perform,
- when these operations were carried out, and
- who was responsible for authorizing those operations.
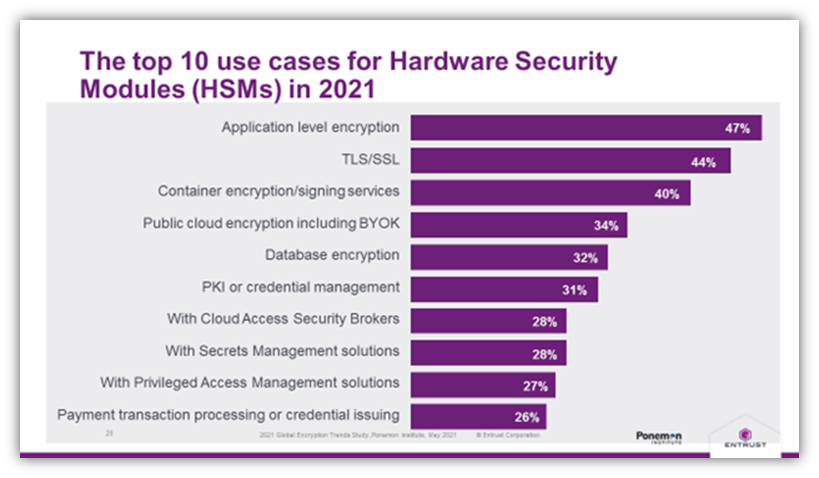
Here’s a breakdown of the top 10 HSM use cases in 2021, according to data from Entrust and the Ponemon Institute:
Hardware Security Module Options: Physical Devices vs Cloud-Based HSMs
Having options for secure cryptographic storage is important for all businesses, particularly as their needs evolve with the growth of their operations. The good news is that HSMs vary in terms of both their physical sizes and applications. Some HSMs are small plug-in cards or USB devices while others are large external devices and appliances that companies store on premises within secure locations.
Hardware security modules can be very cost-prohibitive for many businesses. A 2018 article in SecurityToday.com says that the cost of deploying a single HSM can range upwards of $40,000 — and that price doesn’t include other related costs such as additional hardware, support, and maintenance. So, doing everything yourself may not be a viable option.
But just because your company can’t afford to buy one or more of these devices outright doesn’t mean that you can’t still enjoy the advantages of using HSMs. Some vendors (such as Thales and Amazon Web Services) now offer cloud-based HSM products and services.
There are a few different options when it comes to using cloud HSMs:
- Rent a dedicated physical HSM appliance that gets stored in your off-site data center.
- Pay for access to the functionalities of an HSM vendor’s device or appliance.
- Pay for access to a virtual environment within a vendor’s shared HSM.
The idea here is rather than having to buy an expensive physical appliance that you need to protect on site, you can instead “rent” a dedicated physical appliance or pay for access to the functionalities of one controlled by a third-party vendor for less cost.
As you can imagine, there are advantages and disadvantages to each approach, but you’re ultimately the one who needs to decide which approach is best for your organization or business. Just be sure to carefully read the service level agreement (SLA) to ensure they’re what you need.
Of course, there is a way you can have your cake and eat it, too — meaning that you can use an HSM without having to buy or rent one. This is possible when you partner with a managed PKI (mPKI) service provider. For example, DigiCert is an mPKI provider whose platform was built using an HSM. When you use their platform, you can capitalize on their secure HSM on the backend without having to buy or rent this expensive hardware.
Hardware Security Modules vs Trusted Platform Modules: Are HSMs & TPMs the Same?
If you think that an HSM sounds a lot like a trusted platform module, or TPM, there are a couple good reasons.
- Both HSMs and TPMS are tamper-resistant hardware components, and
- Both devices are examples of hardware roots of trust that protect the services and cryptographic tools that global consumers and businesses use daily.
But are these two devices the same? No. TPMs are device-specific components within individual devices whereas HSMs are external devices with wider applications at handling operations relating to many or all devices and applications across an organization’s network.
TPMs are basically computer chips that physically attach to individual devices’ motherboards to secure their PKI keys while keeping them separate from the devices’ CPU memory. They help to ensure device integrity and provide an isolated environment for the device’s cryptographic operations.
HSMs, on the other hand, are hardware devices that aren’t limited to individual machines. They’re intended for use at-scale by applications and servers across your organization.
To learn more about what trusted platform modules are and how they work, be sure to check out our other article relating to that specific topic.
Who Uses HSMs and Why Are They Important to Your Organization’s Digital Security?
The National Institute of Standards and Technology (NIST) Special Publication “Recommendation for Key Management: Part 2 — Best Practices for Key Management Organizations” (SP-800-57 part 2, rev 1) describes hardware security modules as critical key management components. They’re part of the physical infrastructure that makes secure key storage and cryptographic operations possible.
HSMS are used by organizations across virtually all industries, some of which include:
- Certificate authorities (public and private CAs),
- Government and public sector organizations,
- Cloud service providers and vendors,
- Banks, credit card…
